Some companies have had enough. The cost, lost productivity, inconvenience and bad publicity that come with the numerous data breaches regularly in the news have companies fighting back.
Businesses have figured out how to hack the hackers, and now some in Congress want to give them the legal authority to do so.
Companies that suffer a cyberattack have been going outside their own computer network to track down the hackers, identifying them and publicly shaming them, and doing what they can to undo the mischief. It’s at best a legal gray area, but legislation sponsored by U.S. Rep. Josh Gottheimer of New Jersey would make this obscure practice a legal one in the eyes of the federal government.
“This bill gives specific, useful tools to fight back against cyberattacks that have cost Americans hundreds of millions of dollars, not to mention their personal privacy,” Gottheimer said in a press release with co-sponsor Tom Graves (R-GA).
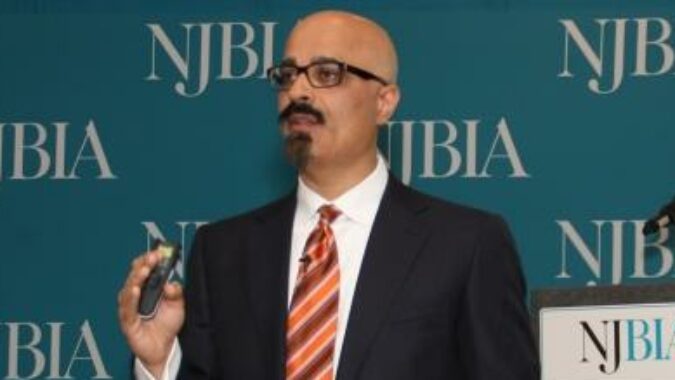
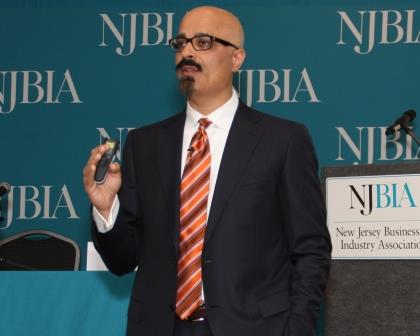
“This is an interesting bill because many companies are already doing this,” explains Rashaad Bajwa of Domain Computer Services in Cranbury. “They are taking active countermeasures to identify and sometimes even penetrate the environment of the hackers that are hacking them. In large part this is because many attacks are from overseas and outside the jurisdiction or capability of local law enforcement.”
Bajwa is an expert on cybersecurity and a regular presenter NJBIA’s cybersecurity events, where he shows businesses how hackers can get access to websites using your phones, computers, laptops, and even EZ Pass.
“The law needs to catch up with technology, and businesses need to be able to defend themselves,” he says. “This bill mostly provides legal cover for these ‘counter hacking’ activities.”
Two of the most common cybercrimes against businesses are data theft and ransomware. Data theft steals personal information of people stored on servers, like credit card numbers, that can be sold to identity thieves or used to commit fraud. Ransomware is a computer virus that locks down a company’s network so that hackers can demand payment in return for opening it back up and letting the business recover its data.